Be On The Lookout For CDC Scams & COVID Phishing Emails
Hackers are taking advantage of the Coronavirus (COVID-19) pandemic with CDC scams by sending out massive amounts of COVID phishing emails. Hackers are offering information regarding the virus pretending to be from a reliable source. Some emails look more legitimate than others. These CDC scams are meant to steal your valuable information or infect your computer networks with malware and/or malicious software. We feel it is our duty to inform water utilities of these possible threats.
Cybercriminals are sending phishing emails out claiming to be trusted sources. The U.S. Centers for Disease Control and Prevention (CDC) and the World Health Organizations (WHO) have both released warnings about the coronavirus phishing emails being sent out around the country.
We have seen a large increase in phishing emails since the start of the virus, stay on the look out for phishing emails and have a sense of what to look out for. If an email you receive has an offer that is way too good to be true or is asking you to do something urgently, it is most likely a phishing email or scam.
How do I know if it’s a CDC scam phishing email or not?
Below is an example of a CDC phishing email claiming to be from the U.S. Centers for Disease Control and Prevention.
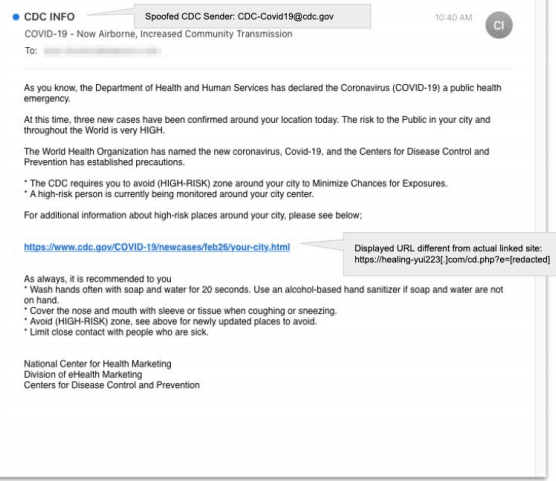
CDC COVID-19 Phishing Email
“As you know, the Department of Health and Human Services has declared the Coronavirus (COVID-19) a public health emergency.
At this time, three new cases have been confirmed around your location today. The risk to the Public in your city and throughout the World is very HIGH….
For additional information about high-rise places around your city, please see below.
(link)”
People fall for these schemes so often due to how legitimate these phishing email looks. This outbreak is a dream come true for cybercriminals. Everyone has an abundance of interest and concern about the coronavirus, that people will practically open anything regarding the virus. All it takes is one single click on a link where you then land on a site where hackers take full control. At that point, malicious actors will have access to all of your emails and passwords.
How to spot a phishing email:
- It is rare for organizations to ask for credit card numbers, passwords or any type of personal information over an email. Always verify by calling the company if you are unsure before giving away any information.
- Most of these COVID phishing emails tend to use a very generic salutation, like “Dear Mam,” or “Dear Sir,”.
- Look at the email address of the sender. Use your cursor to hover over the ‘from’ email address. Check the email address to see if it has been changed in any way. For example: bill@paypal.com to bill@paypal73.com.
- Organizations will not send random file attachments. Hackers will direct you in the email to download the attached documents or files that contain malware. This is a common technique used by malicious actors.
- Check the URL by hovering over the link with your cursor. If the link in the text is the same as the URL displayed when the cursor hovers on the link, that is a sign that it is most likely a legitimate link.
- Check the grammar on the email. Cyber criminals are known to have small spelling or grammatical errors throughout their phishing emails.
Make sure your utility is aware of the CDC scams and COVID phishing emails, cybercriminals are preying on the fear of the pandemic. Make sure you, your friends and coworkers are all educated on how to recognize and spot phishing emails. Remember to never click on a link in a email you are unsure of.
For the latest information on the COVID-19 pandemic, go to the CDC website.
